Access control is a vital part of information security and is defined as the process by which you grant or deny access to your data, property, and other objects. Three elements make up access control: identification, authentication, and authorization.
The world of information security is vast. There are many different kinds of attacks and various defenses against them. One type of defense is an access control system with policies that define who has the right to do what within a given system or environment.
Access control systems typically consist of identifiers (such as usernames), authentication methods (such as passwords), and authorization processes to determine whether an authenticated user should be allowed or denied access to something based on their identity and the result from the authentication process. All access control systems aim to prevent unauthorized users from accessing confidential data stored in protected computers, networks, databases, or other digital media.
Elements of Access Control
Identification
Identification is the process of determining who someone is and verifying their identity. It's not always easy, especially when dealing with large groups of people in a short span of time.
Users must be uniquely identified before they can be verified and authorized to access resources. The two main methods of identification are user IDs and badges.
- User IDs - User IDs are unique identifiers assigned to each user in the system. They are used to track user activity and tie access to specific individuals. User IDs should be difficult to guess and should not contain any clues about the user's identity or role. IDs are often tied to accounts and profiles that contain additional user information.
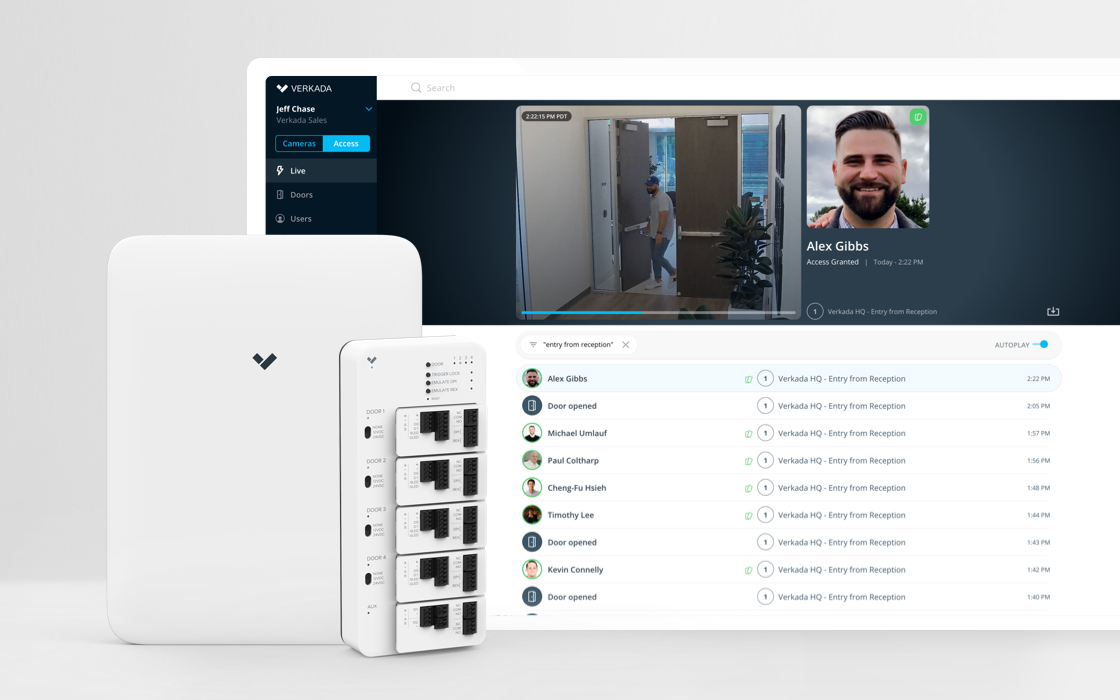
- Badges B. - Badges serve as physical identification. They are cards or tags worn visibly by users. Badges allow security personnel to quickly identify authorized individuals. The badge often includes a photo, name, and organization for visual verification. Badges enable access control in physical spaces by integrating with card readers on doors.
Authentication
Access control limits access to information and data, depending on the person's role, identity, or authorization level. Authentication is one part of this process; it makes sure the user is who they say they are. Authentication schemes are the backbone of access control. They are responsible for verifying who you are and what you're allowed to do once authenticated.
After identification, users must authenticate themselves. Authentication proves the user is who they claim to be. It is commonly implemented through passwords and biometrics.
- Passwords - Passwords are secret words or phrases used to authenticate user identities. They should be strong enough to resist guessing and brute force attacks. Strong password policies enforce minimum length, complexity, and periodic changing of passwords. Multifactor authentication can be implemented by requiring a password plus a one-time code sent to the user.
- Biometrics authentication - Biometrics authenticate users based on unique physical characteristics. Examples include fingerprints, retina and iris scans, facial recognition, and voice recognition. Biometrics provide a convenient hands-free authentication and higher security than passwords alone. However, biometric systems require specialized scanners and enrollment of user biometrics.
Authorization
Authorization is the means of regulating who can access what. The two types of authorization are discretionary and mandatory. Discretionary authorizations are granted by an entity, such as an owner or administrator, to individuals based on their need to protect the resource from unauthorized access. Mandatory authorizations are granted to people with common needs while being protected from unauthorized access.
Once identified and authenticated, users must be authorized to access specific resources. Authorization defines the user's permissions within the system. Two common methods are access control lists and role-based access control.
- Access control lists - Access control lists outline exactly which resources a user can access. Permissions are assigned to the user's unique ID. While flexible, ACLs can be complex to manage as permissions change.
- Role-based access control - Role-based access control grants access based on the user's role within the organization. Roles come with predefined permissions, making user administration simpler. However, defining roles with the proper permissions requires careful planning.
Challenges of Access Control
Implementing and managing access control systems comes with a unique set of challenges. Organizations must balance security and usability, manage complexity, and stay on top of emerging threats. Failing to address these challenges can render access control measures ineffective.
Balancing Security and Usability - Security teams want extensive access control systems to protect information and resources. However, highly restrictive controls hamper user productivity and experience. Organizations must strike a balance between security and usability.
Overly complex password requirements or multi-factor authentication frustrate users, yet weak credentials leave systems vulnerable. Biometrics improve usability but have drawbacks like error rates. Security leaders must collaborate with users and stakeholders to develop reasonable controls.
Managing Complexity - Sophisticated access control means managing intricate layers of interconnected policies, procedures, and technologies. Keeping authorization rules up to date across numerous applications and diverse user populations is complex.
Maintenance and auditing at scale requires centralized access control platforms. Automation handles routine provisioning and deprovisioning tasks. Teams must regularly review policies, strip old permissions, and monitor for anomalies indicating compromised accounts.
Addressing New Threats - Threat actors constantly evolve new techniques to bypass access controls through phishing, social engineering, credential stuffing, and password spraying attacks. Machine learning and behavioral analytics help spot suspicious access patterns. Zero trust access models dynamically verify user identities and limit lateral movement after breaches. Organizations must continually assess and upgrade controls to detect and deter advanced attacks. Failing to address these access control challenges will undermine security efforts.
Access control presents unique management and technical challenges. Organizations can overcome them through balanced usability-focused design, automation, and an adaptable threat-aware strategy. What challenges have you faced in implementing access controls? Please share your experiences and thoughts below.
The next time you consider upgrading your access control system, consider the elements we've outlined here. Some of them may be difficult to implement for your organization, and others not so much. By understanding these different features, you can decide on the best solution for your needs. Contact us at BCS Consultants to find the best option for your business.