Protecting a business is more than just locking the doors at the end of the day. With rising threats to commercial spaces—from break-ins and theft to vandalism—business owners are prioritizing security more than ever. That’s where intrusion alarm systems come in.
Comprehensive guide to warehouse security camera systems

Warehouses are vital to supply chains, managing large inventories and constant movement. Securing these complex spaces requires advanced solutions—and none are more critical than implementing reliable warehouse security cameras. These systems serve as the backbone of modern warehouse security and operational oversight.
The Key Benefits and Considerations of Integrated Access Control

Physical security remains a critical aspect for businesses of all sizes, especially as security threats continue to evolve. Companies need robust, flexible, and smart security solutions that seamlessly adapt to their changing needs. Integrated access control systems have emerged as a superior solution, offering a smarter, scalable approach to managing security.
Balancing Innovation and Privacy: How Facial Recognition Technology Is Evolving with Responsibility
As facial recognition technology (FRT) becomes more widespread in everyday life—from smartphones and lobby access to airport security checkpoints—it’s no longer a question of if businesses will adopt this technology, but how they can do so responsibly.
Guide to key card access control systems and door locks for businesses

Business security is no longer a luxury—it's a necessity. From protecting intellectual property and sensitive data to ensuring employee safety, robust security systems are essential for any organization. Businesses must have reliable access control systems that not only secure their premises but also streamline day-to-day operations.
4 Best Small Business Security Systems to Consider

For small businesses, security is not just a concern—it’s a necessity. From protecting assets and employee well-being to safeguarding sensitive data, having reliable small business security systems can make all the difference in reducing risks. The right small business security solutions provide protection against theft, unauthorized access, and other vulnerabilities that businesses face daily.
Complete guide to commercial access control systems for office buildings
What is Low Voltage Wiring & Cabling? Full Guide
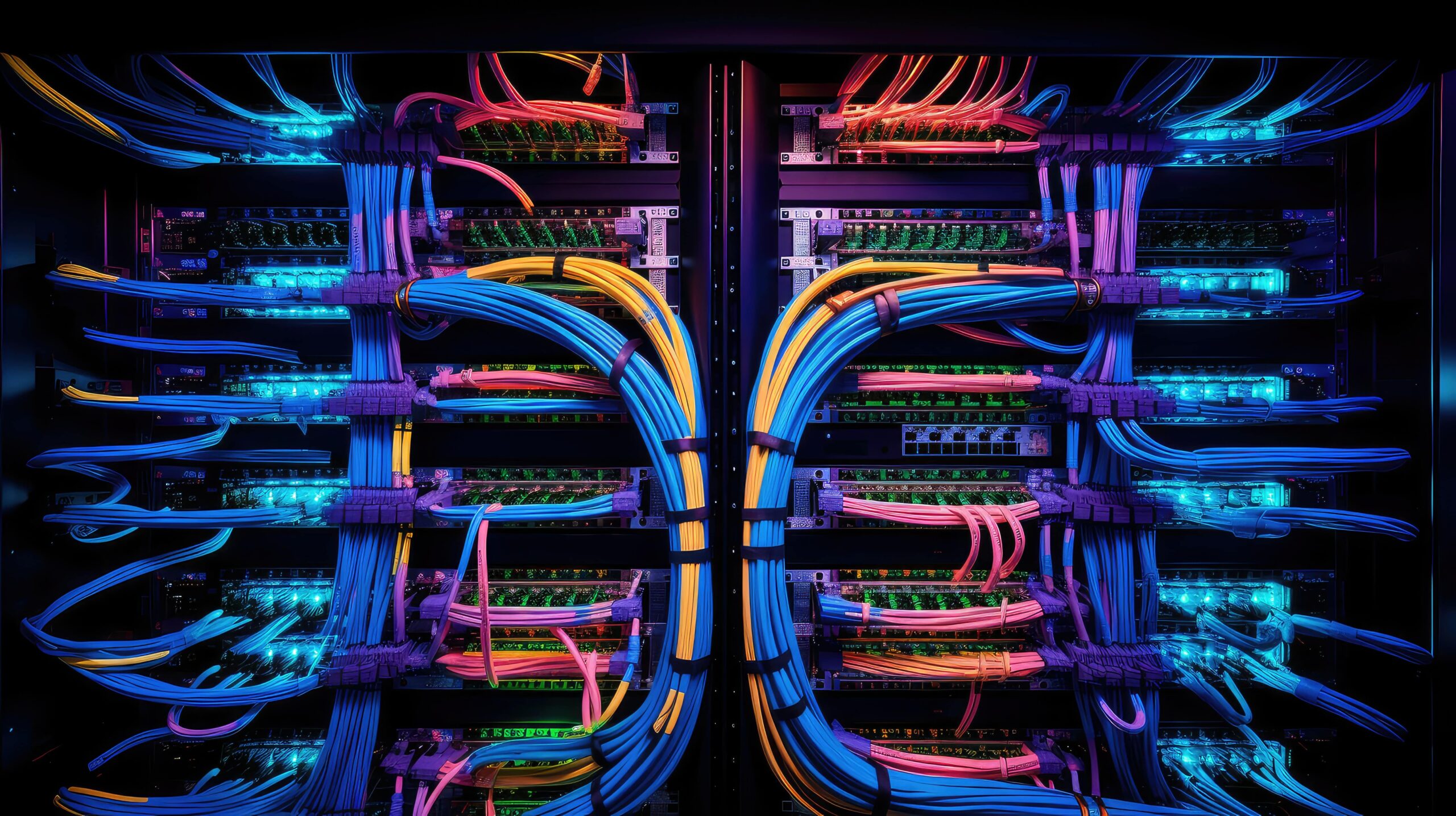
Picture this: you walk into a sleek office where video calls run seamlessly, security cameras keep an eye on everything, and lights adjust automatically to the perfect brightness. Behind this seamless operation lies the magic of low voltage installation, ensuring everything functions smoothly and efficiently.




