Introduction to Modern Access Control
Security threats are no longer limited to physical break-ins or stolen keys. Organizations now face a mix of physical intrusion, insider risk, credential theft, and cyber-enabled attacks that blur the line between IT and facility security. This shift has pushed Access Control Technology to the center of modern security planning.
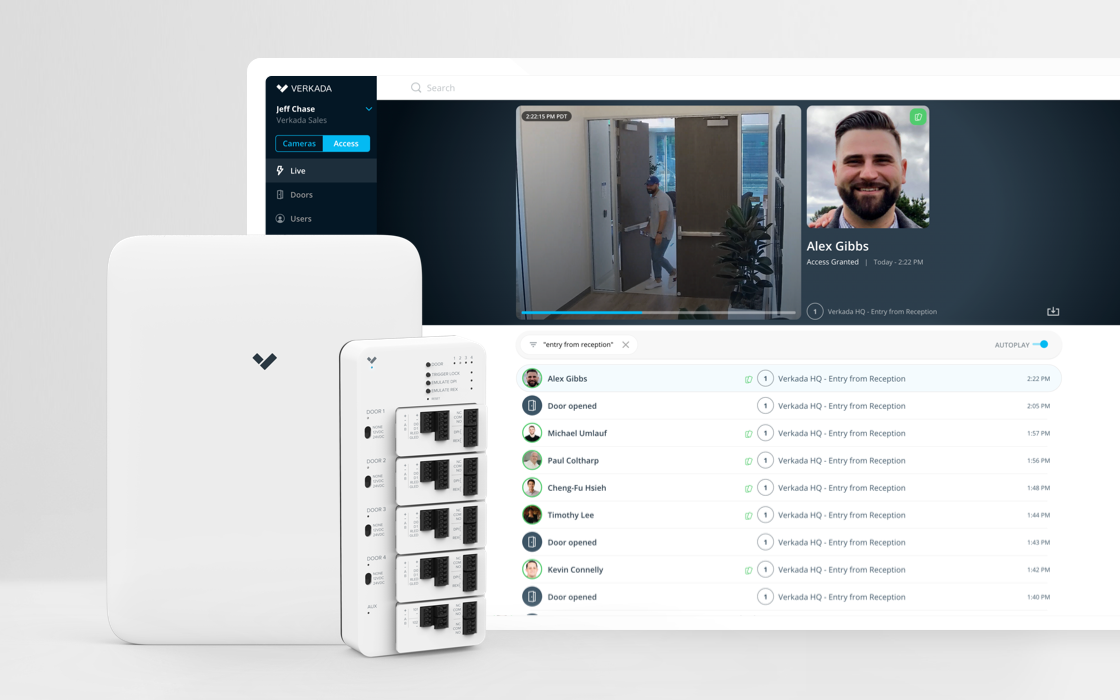
New access control technology refers to digital, intelligent systems that manage who can enter a space, when they can enter, and under what conditions. These systems go far beyond traditional locks and keycards. They combine identity verification, software-driven policies, real-time monitoring, and integration with broader security infrastructure.
This guide breaks down how access control has evolved, the technologies shaping today’s systems, and how businesses can make informed decisions as they plan upgrades. You will also see real-world examples, trade-offs, and future trends shaping the Future of Security Systems.
The Role and Importance of Access Control in Security Systems
Access control acts as the first line of defense in any security architecture. It determines who gets in and who stays out, both physically and digitally. Without strong access control, even the most advanced cameras or alarms only record incidents instead of preventing them.
Modern access control systems help reduce several critical risks:
- Unauthorized physical entry into restricted areas
- Insider threats caused by shared or stolen credentials
- Theft of assets, data, or sensitive equipment
- Compliance failures related to audit trails and accountability
Access control also works best as part of a layered security model. It complements video surveillance, intrusion detection, and monitoring platforms by limiting access before an incident occurs. When integrated properly, access control systems can trigger alerts, activate cameras, or lock down areas automatically in response to suspicious activity.
Evolution of Access Control Technology
Access control has changed significantly over the last few decades, driven by advances in electronics, networking, and data analytics.
Traditional Access Methods
Early systems relied on mechanical locks and physical keys. While simple, these methods created major risks. Keys could be copied, lost, or shared, and there was no record of who accessed a space.
Electronic Access Control
The next phase introduced electronic locks, keypads, and card readers. PIN codes and proximity cards improved accountability, but they still relied on something a user had or remembered. Lost cards and shared PINs remained common issues.
Smart and Intelligent Systems
Today’s Access Control Technology moves toward identity-driven security. Biometric verification, mobile credentials, cloud platforms, and intelligent analytics allow organizations to manage access dynamically. Permissions can be updated instantly, access can be revoked remotely, and every interaction is logged for review.
Key Emerging Technologies in Access Control
This section forms the core of modern access control strategy. Each technology addresses different operational and security needs.
Biometric Systems
Biometric Access Control relies on physical or behavioral characteristics to verify identity. Common methods include fingerprints, facial recognition, and iris scanning.
Benefits
- Credentials cannot be lost or shared
- Faster authentication for high-traffic environments
- Strong identity assurance for sensitive areas
Challenges
- Privacy and data protection concerns
- Environmental limitations such as lighting or sensor quality
- Higher upfront deployment costs
Best practices include encrypting biometric data, following regional privacy laws, and using biometrics alongside secondary authentication methods for critical zones.
Mobile and Credential-Based Access
Mobile Access Control replaces physical cards with secure digital credentials stored on smartphones. Technologies like NFC and Bluetooth allow users to unlock doors using approved mobile apps.
Advantages
- Remote credential issuance and revocation
- Reduced cost of lost cards
- Better user convenience and flexibility
This approach is especially effective for distributed teams, temporary access needs, and facilities with frequent staff changes.
Cloud-Based Access Control
Cloud-Based Access Control moves system management and data storage off local servers and into secure cloud environments.
Key benefits
- Centralized management across multiple locations
- Automatic updates and reduced maintenance
- Scalable architecture that grows with the organization
Cloud platforms also simplify compliance reporting and disaster recovery by keeping access records securely backed up.
AI and Machine Learning in Access Control
AI-Powered Access Control introduces intelligence into decision making. These systems analyze patterns in access behavior and identify anomalies that may signal threats.
Examples include:
- Detecting unusual access times
- Identifying repeated failed entry attempts
- Adjusting permissions based on behavior patterns
AI systems improve security posture over time, but they require quality data and careful configuration to avoid false positives.
IoT Integration
IoT in Security Systems allows access control platforms to interact with cameras, sensors, lighting, and building automation tools.
Integrated systems can:
- Lock doors automatically during emergencies
- Trigger alerts when doors are forced open
- Adjust lighting or HVAC based on occupancy
This level of automation improves response time and situational awareness.
Blockchain and Secure Logging
Blockchain technology introduces immutable access logs that cannot be altered after creation. This capability supports compliance, investigations, and transparency.
Use cases
- High-security facilities
- Regulated industries
- Environments requiring tamper-proof audit trails
While still emerging, blockchain-based logging shows promise for accountability-driven security programs.
Advantages and Trade-offs of Each Technology
Every access control technology comes with strengths and limitations.
Security and Accuracy
Biometric and AI-driven systems offer high accuracy but require careful planning around privacy and system tuning.
Convenience and User Experience
Mobile credentials and cloud platforms improve usability but depend on reliable network access.
Scalability and Cost
Cloud-based solutions scale easily, while on-premises systems may demand higher long-term maintenance.
The best approach often involves combining multiple technologies to match operational needs rather than relying on a single solution.
How a Consultant or Security Expert Can Guide the Selection
Choosing the right Access Control Technology requires more than product comparison. A security consultant brings structure and experience to the process.
Key steps include:
- Assessing facility layout, risk profile, and user volume
- Reviewing regulatory and compliance requirements
- Planning integration with cameras, alarms, and building systems
- Designing hybrid or cloud-based architectures
- Evaluating vendors based on reliability and support
- Managing deployment, training, and adoption
- Conducting regular audits and system updates
Expert guidance helps avoid costly mistakes and future rework.
Real-World Examples and Case Studies
Enterprise Upgrade Example
A corporate campus replaced card-based systems with Biometric Access Control combined with Cloud-Based Access Control. The result was reduced credential misuse, faster onboarding, and centralized oversight across locations.
Integrated Facility Example
A logistics facility connected access control with IoT sensors and AI-Powered Access Control analytics. Automated lockdowns and real-time alerts reduced response times during security incidents.
Both cases highlight the importance of integration planning and staff training.
Future Trends and What’s Next
The Future of Security Systems points toward more adaptive and identity-centric models.
Emerging directions include:
- Context-aware access decisions based on location and behavior
- Deeper alignment with identity and access management frameworks
- Stronger focus on zero-trust security principles
- Development of quantum-resistant encryption methods
Regulatory pressure and evolving threats will continue to shape how access control systems are designed and deployed.
Ready to Plan Your Access Control Strategy?
Modern Access Control Technology demands more than hardware selection. It requires clear risk assessment, system design expertise, and the ability to integrate access control with cameras, alarms, and building infrastructure.
BCS Consultants helps organizations evaluate current security gaps, design scalable access control architectures, and implement systems that support long-term operational and compliance needs. From biometric systems and cloud-based platforms to AI-driven analytics and IoT integration, our consultants guide every phase of the process with clarity and precision.
If you are considering an upgrade or planning a new deployment, speak with a BCS Consultants security expert to discuss your facility requirements and next steps.
Contact BCS Consultants today +1 (949)-304-6036 to schedule a security consultation and begin building a smarter access control framework.
Frequently Asked Questions
What is Access Control Technology and how does it improve security?
Access Control Technology manages who can enter a physical or digital space based on verified identity, permissions, and rules. Modern systems replace keys and static cards with biometrics, mobile credentials, and software-driven policies. This reduces unauthorized entry, improves accountability, and creates detailed access records for audits and investigations.
How does Biometric Access Control compare to card or PIN-based systems?
Biometric Access Control uses physical traits like fingerprints or facial recognition, which cannot be lost or shared. Card and PIN systems rely on items or knowledge that can be stolen or reused. Biometrics provide stronger identity verification, though many organizations combine them with Multi-Factor Authentication (MFA) for higher-risk areas.
What are the benefits of Cloud-Based Access Control for growing organizations?
Cloud-Based Access Control allows centralized management of multiple locations from a single dashboard. Administrators can issue or revoke access remotely, apply policy updates instantly, and maintain secure audit logs without on-site servers. This approach supports scalability, remote operations, and easier system maintenance.
How do AI and IoT improve modern access control systems?
AI-Powered Access Control analyzes behavior patterns to detect anomalies, such as unusual access times or repeated entry failures. IoT in Security Systems connects access control with cameras, sensors, lighting, and alarms. Together, they enable automated responses, faster incident detection, and more informed security decisions.